The Center East area is rapidly rising as a brand new, dynamic participant on this planet of cybersecurity rules. As nations within the area diversify their economies past the standard oil and fuel sectors and embrace a digital future for its residents and residents, new rules, legal guidelines and frameworks are being launched to make sure safety within the new digital world.
These frameworks, geared toward bolstering the cybersecurity practices throughout many private and non-private sector organizations, introduce a number of obligatory controls and threat administration practices that are required for varied companies working within the area with the intention of accelerating cyber resilience.
As a member of Cisco Talos Incident Response, we frequently get to function inside these frameworks when partaking with our clients throughout Emergency Response actions or throughout proactive engagements similar to Desk High Workouts, IR Playbook or IR Plan creations.
This weblog will delve into the evolution of those rules, inspecting the catalysts that prompted their inception and the next influence on shaping the digital panorama.
State of Qatar
The State of Qatar’s cybersecurity regulatory framework consists of legislations, worldwide requirements and technique pointers positioned inside varied cybersecurity frameworks, launched throughout completely different strategic and enterprise sectors. The first physique, chargeable for cybersecurity insurance policies, throughout the State of Qatar is the Nationwide Cyber Safety Company (NCSA) which was established in 2021 to facilitate the event and proposal of cybersecurity insurance policies and rules throughout the nation. A number of items of laws cowl the cybersecurity of IT techniques and private knowledge and are straight relevant to completely different cybercrime legal guidelines. There are two key legal guidelines relevant within the State of Qatar are:
- Cybercrime Prevention Regulation (2014): This cornerstone regulation criminalizes varied cyber offenses, together with unauthorized entry, identification theft and on-line fraud. It prescribes penalties and descriptions investigative procedures associated to the aforementioned crimes.
- Private Knowledge Safety Regulation (PDPL) (2016): This regulation grants people management over their private knowledge, requiring organizations to acquire consent, implement safety measures, and reply to knowledge topic requests. This regulation can also be supported by a number of further procedural pointers, defining how a few of the particular implementation of varied controls, notifications and processes, that are relevant when private knowledge is acquired and processed, must be utilized. For instance, there’s a requirement for knowledge breaches to be reported to the Nationwide Cyber Governance and Assurance Affairs (NCGAA) and affected people inside 72 hours of changing into conscious of the breach.
Whereas these legal guidelines intently guard varied cybersecurity points associated to enterprise and people, Qatar’s cybersecurity panorama additionally consists of a number of frameworks and pointers relevant throughout the nation. Three are described beneath:
The Nationwide Cybersecurity Technique (2014)
Launched in 2014, this doc outlines initiatives undertaken by the Qatari authorities to guard key belongings and determine dangers associated to essential data infrastructure (CII). The general technique focuses on 5 fundamental targets, starting from constructing safeguards for the CII to establishing authorized frameworks that create a safer our on-line world. It additionally consists of methods targeted on establishing a collaborative setting geared toward constructing and cultivating nationwide cybersecurity capabilities. The general theme of this technique is predicated on the understanding that cybersecurity is a shared duty, and that many authorities entities, companies and people want to come back collectively to create an setting that’s resilient to cybersecurity incidents. The important thing controls, established inside this framework, will be damaged down between private and non-private sector duties. The state, for instance, points legislations such because the Cybercrime Prevention Regulation (2014) or Private Knowledge Safety Regulation (2016) that every one people and organizations in Qatar must be following. Then again, organizations can straight handle the outlined technique by making use of the next controls throughout a number of key pillars:
Safeguard nationwide Vital Info Infrastructure (CII)
- Controls that may be utilized to assist this pillar embrace vulnerability assessments, creation of incident response plans and threat administration frameworks, which might define how threat is handled inside a corporation and which mitigation controls should be utilized to CII organizations.
Implement environment friendly incident response mechanisms and restoration proceedures
- Controls that may be utilized to assist this pilar embrace establishing of data sharing platforms, similar to risk intelligence trade platform, the flexibility to invoke or have the flexibility to coach emergency response groups and have acceptable harm evaluation protocols, which would cut back the consequences of widespread assaults on CII infrastructure.
Develop and domesticate nationwide cybersecurity capabilities: Construct a talented workforce, spend money on analysis and improvement and strengthen nationwide cyber protection capabilities
- Controls which will be utilized to assist this pilar embrace establishing cybersecurity education schemes, expertise recruitment initiatives and analysis partnerships, which could deliver further data associated to how revolutionary cybersecurity frameworks and technical improvements will be deployed throughout organizations.
Qatar Cybersecurity Framework (QCF) (2018)
Developed by the Supreme Committee for Supply & Legacy (SCDL) forward of the 2022 FIFA World Cup, the QCF supplies a set of greatest practices and controls for organizations to boost their cybersecurity posture when taking part in main occasions. Controls are mapped to varied worldwide requirements similar to ISO 27001, NIST SP 800-53, ISA62443, PCI-DSS and GDPR. The main focus of the framework is predominantly on 14 completely different capabilities starting from establishing an acceptable governance to utility of safety controls within the cloud.
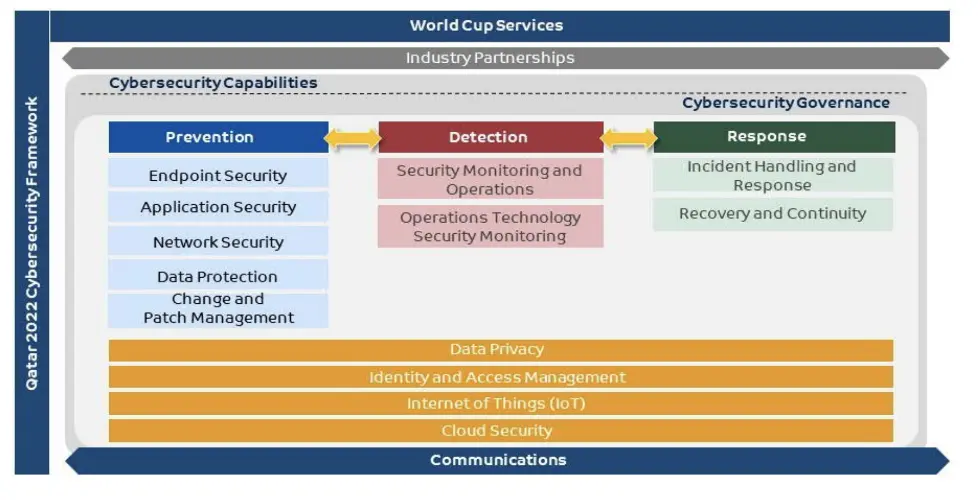
This framework launched the necessity to have a broadly established threat administration methods that handle technical controls, similar to making certain that threats will be detected on all method of gadgets similar to laptops or servers (requirement 3.2), and capabilities to determine, audit, remediate and check varied safety methods, similar to hardening of the techniques, minimizing dangers via institution of related inside frameworks and controls that additionally depend on presence of acceptable workers (i.e., necessities 4.2 and 5.2). Varied controls and evaluation necessities are additional damaged down into main domains with every presenting necessities for the way profitable controls must be deliberate, deployed, managed and managed all through the lifetime of an occasion. The place possible, particular components of an QCF are mapped to controls current in different requirements similar to Nationwide Info Assurance Commonplace or ISA62443.
Nationwide Info Assurance Commonplace (NIAS) (2023)
This latest customary launched a number of controls to technical, enterprise and governance points of any group working within the State of Qatar, together with third events and subcontractors which are particularly known as out within the scope of the usual (part 2.2). The usual focuses on key areas similar to knowledge governance, knowledge safety, technical and group controls. It prioritizes 4 key ideas:
- Confidentiality: Guaranteeing solely licensed people entry data.
- Integrity: Guaranteeing knowledge accuracy and completeness.
- Availability: Making data accessible when wanted.
- Accountability: Holding people chargeable for cybersecurity.
One other vital side of the usual is the requirement to categorise the information that’s saved throughout the group and the requirement to guard such knowledge with particular controls that are relevant although proactive threat administration. It must be famous that this customary operates at the side of Nationwide Knowledge Classification Coverage (2023) to create a synergy between data safety and knowledge classification. Every area and management set have a set of obligatory and elective controls which leaves a scope for flexibility in how controls could be utilized inside a given group, as not each potential area could be relevant, or it could be relevant simply partially. Though organizations can apply the usual on a voluntary foundation, the Nationwide Cyber Safety Company additionally affords a certification course of which assesses the compliance with the usual.
The Nationwide Cyber Safety Technique (2024)
Launched in 2024, this technique doc builds on the framework established in 2014 and emphasizes the centralization of safety governance beneath a single group, the NCSA. The framework is guided by six ideas, starting from shared duty, the place everyone seems to be accountable for his or her cybersecurity practices, to a concentrate on collaboration and coordination amongst varied stakeholders in Qatar’s cybersecurity panorama. These guiding ideas underpin the 5 pillars of the framework, every linked to particular strategic targets, together with constructing a resilient cybersecurity ecosystem and fostering laws and innovation in a data-driven financial system. Every pillar will be additional damaged down into particular targets that can information each personal and public organizations in attaining higher safety maturity via accreditations, schooling, analysis, improvement, and innovation in cybersecurity purposes. Whereas some targets and pillars concentrate on home improvement, there’s additionally a powerful emphasis on forming regional and worldwide partnerships.
Kingdom of Saudi Arabia
Equally to the State of Qatar, the Kingdom of Saudi Arabia (KSA) have launched legislations and frameworks aiming to make sure that cybersecurity utility is as widespread as potential and relevant throughout as many sectors as potential according to the digitization targets. Safety from digital threats is likely one of the targets of Imaginative and prescient 2030 which places emphasis on digital society dwelling in a protected our on-line world supported by the Kingdom’s e-government. The 2 key legal guidelines relevant within the Kingdom of Saudi Arabia are:
- Anti-Cyber Crime Regulation (2007): This regulation is a essential piece of laws in Saudi Arabia aiming to stipulate penalties for widespread cybercrime actions similar to knowledge theft, unauthorized entry, cyber assaults, identification theft and impersonation.
- Private Knowledge Safety Regulation (2023) (PDPL): The PDPL regulates knowledge topic rights and grants them the appropriate of management over their knowledge in addition to defines the position of information controllers, which have entry to private knowledge within the Kingdom of Saudi Arabia. As this regulation is sort of new, the grace interval for compliance runs till Sept. 14, 2024, when knowledge controllers might want to adjust to outlined obligations. This regulation affords a variety of rights and duties, that are afforded to people similar to the flexibility to entry, rectify, erase and limit processing of their private knowledge together with breach report obligations inside 72 hours.
As a part of the Nationwide Cybersecurity Technique (NCS), the Nationwide Cybersecurity Authority (NCA) was established in 2017 to control and enhance the cybersecurity panorama within the KSA with the target to supervise the appliance and improvement of cybersecurity rules throughout the Kingdom. The strategic positioning of the NCA permits it to not solely create authorized, coverage and regulatory environments, however actively take part and interact with regulated our bodies via assessments or help with data sharing exchanges and different relevant partnerships.
The NCA carries out main duty for improvement and the appliance of varied controls and frameworks throughout completely different verticals within the KSA and breaks down a number of shared duties into frameworks, which collaborate at varied ranges in the private and non-private sectors.
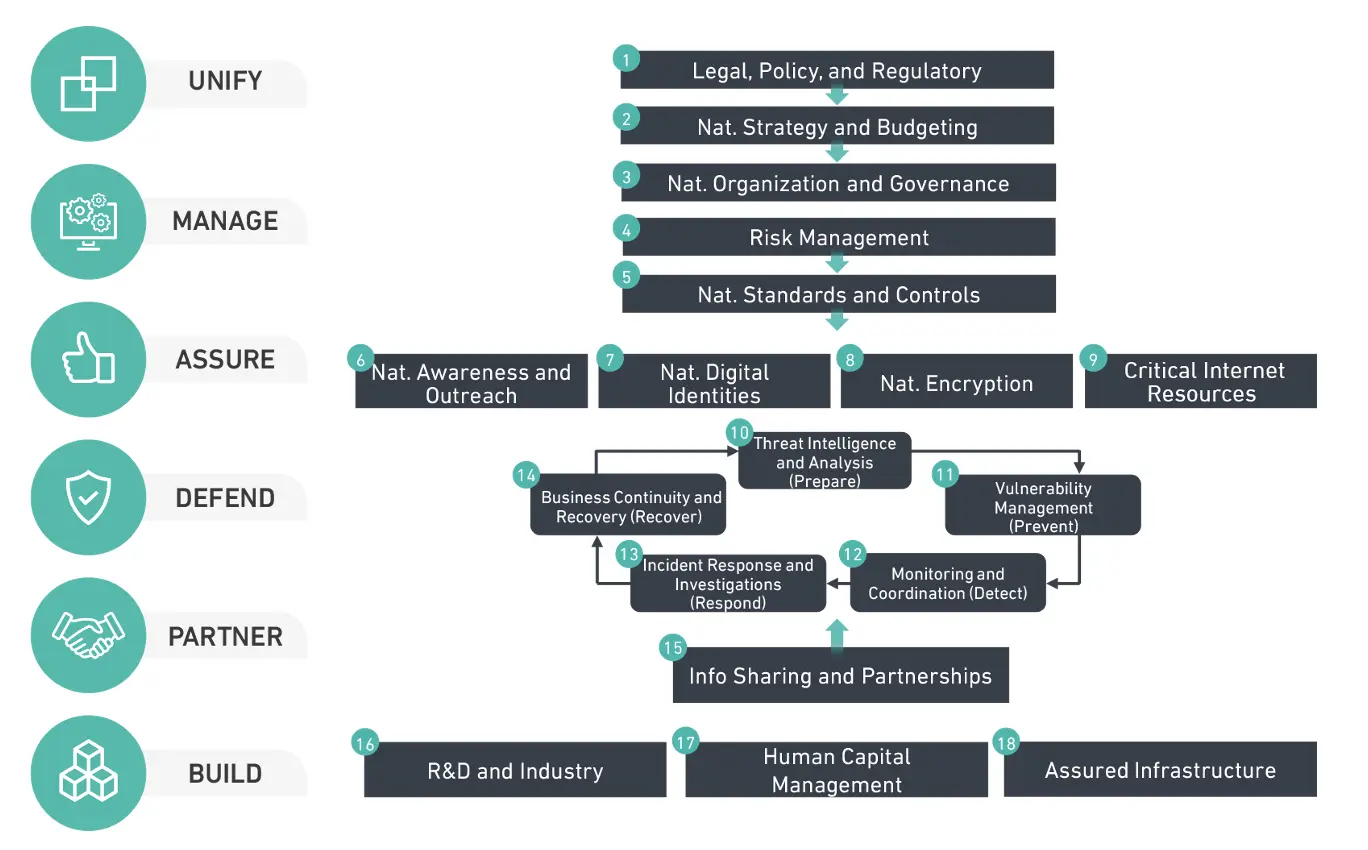
Nationwide Cyber Safety Technique (NCSS) (2019)
The NCSS is a cornerstone technique that outlines a number of key ideas that the Kingdom of Saudi Arabia will comply with to boost the nation’s cybersecurity. The strategic targets of the NCSS are to unify cybersecurity governance beneath one physique (the NCA), create a partnership setting to collaborate and carry out cybersecurity analysis, defend the nation from cyber threats and construct nationwide and business cybersecurity capabilities. The NCSS outlines how the Kingdom will strategy the event of cybersecurity sooner or later and units out administrative management over this course of.
Important Cybersecurity Controls (ECC) (2018)
Outlines a set of obligatory minimal cybersecurity necessities for organizations, private and non-private, working throughout the Kingdom of Saudi Arabia. These controls function the inspiration for shielding essential infrastructure, authorities companies, and personal companies from cyberattacks and threats. There are 114 completely different controls established throughout 5 fundamental domains:
Cybersecurity Governance
Focuses on institution of mechanisms that that drive the adoption of cybersecurity measures. The important thing controls deployed inside this customary are:
- Establishing correct management roles and duties for cybersecurity inside a corporation.
- Emphasize the event of a strong safety technique aligned with the enterprise roadmap.
- Guaranteeing assist from acceptable personnel to outline clear procedures for cybersecurity threat administration that may be executed although sturdy mission administration.
- Upkeep of compliance with current rules.
Cybersecurity Protection
Focuses on constructing controls to guard techniques and networks from unauthorized entry, malware, and different threats. The important thing management on this part begins with establishing an in depth asset register, which highlights gadgets in danger, among the many gadgets owned by the enterprise and ensures that acceptable visibility is granted to techniques beneath administration. These controls are available in many varieties similar to making certain that identification entry, cellular gadgets, perimeter, and community gadgets are properly configured, hardened and segregated. Along with constructing technical controls, this doc additionally focuses on making certain that course of perspective is considered and so, there are a number of necessities round, for instance, penetration testing, incident response and vulnerability administration, and the way a majority of these engagements must be carried out.
Cybersecurity Resilience
Focuses on constructing measures to get well from cyber assaults and reduce disruptions to ongoing operations although a requirement for Enterprise Continuity Administration (BCM) and making certain that acceptable enterprise continuity processes are created and will be adopted in an occasion of a significant enterprise catastrophe.
Third-party and Cloud Computing Cybersecurity
Addresses safety concerns ensuing from partaking with third events or cloud companies. With regards to third events, which could increase cybersecurity capabilities of a corporation, there are particular necessities associated to non-disclosure agreements (NDAs), communication cadence and the necessity for third events to adjust to organizational insurance policies. Cloud computing side of this area, alternatively, requires creation of acceptable insurance policies, classification of information that might be uploaded to the cloud and separation of cloud environments internally from different tenants. ECC requires storage of the information contained in the Kingdom of Saudi Arabia.
Industrial Management Methods Cybersecurity
Addresses controls relevant to industrial management techniques (ICS) and demanding infrastructure (CI). This a part of the ECC Commonplace requires creation of a strictly segmented ICS setting that might be constantly monitored for potential incidents and security. Configuration and hardening are additionally required, together with patch and vulnerability administration processes, which have to be applied to make sure that cybersecurity is upheld inside ICS deployment.
Vital Methods Cybersecurity Controls (CSCC) (2019)
CSCC is an extension to the ECC offering further steerage in direction of organizations that function or personal essential techniques. To be compliant with CSCC, the ECC necessities additionally should be fulfilled. There are 32 different fundamental controls utilized throughout related domains as within the ECC customary. CSCC locations emphasis on the need to make sure that the controls, deployed and configured in alignment with the ECC, bear a rigorous testing course of. This entails common assessments to evaluation relevant safety configurations and handle any recognized deficiencies. The overarching objective is to take care of a strong cybersecurity framework by constantly testing and validating the effectiveness of the applied controls in accordance with the ECC customary and including further layer of verification or further controls.
Cloud Cybersecurity Controls (CCC) (2020)
Equally to CSCC, the CCC controls are an extension of the ECC and purpose to offer a set of minimal necessities, which cloud service suppliers (CSP) and cloud service tenants (CST) must fulfil to make sure that knowledge, saved within the cloud, is protected. This framework divides controls into these relevant to cloud service suppliers and cloud service tenants. Whereas some controls are similar, the final theme of the framework places a requirement for suppliers to tell tenants about cybersecurity controls which are relevant to knowledge saved within the setting, and for tenants to have relevant insurance policies which they’ll evaluate and contract with controls offered by CSP. There are also strict necessities on controls similar to personnel vetting, knowledge storage and disposal, entry and insurance policies and procedures that should be created and utilized to cloud belongings.
Sultanate of Oman
The Sultanate of Oman began to look at their cybersecurity practices in 2010 with the creation of the Oman Laptop Emergency Readiness Staff (OCERT), which screens cyber threats, investigates incidents and supplies steerage to organizations based mostly on the most recent cybersecurity legal guidelines and requirements relevant within the nation. The legal guidelines which are relevant within the Sultanate of Oman assist Oman’s Imaginative and prescient 2040, which places a powerful emphasis on digital transformation and presence of expertise throughout the financial system. The 2 key legal guidelines relevant within the Sultanate of Oman are:
Private Knowledge Safety Regulation (PDPL) (2023)
Oman’s flagship knowledge safety regulation, granting people rights over their private knowledge and imposing obligations on organizations dealing with the information. When it comes to utility, organizations should undertake knowledge safety measures according to the PDPL, together with acquiring consent, implementing safety controls and responding to knowledge topic requests.
Cyber Crime Regulation (2011)
This cornerstone regulation criminalizes the unauthorized entry, modification or destruction of information and different widespread cybercrime similar to fraud or violation of privateness.
The next pointers and requirements, aimed largely at authorities and public-sector entities, can be found within the Sultanate of Oman:
Primary Safety Controls (BSC) (2017)
The BCS controls requirements define the set of fundamental and crucial safety controls that must be utilized throughout authorities organizations in Oman. Beginning with entry management, the usual breaks down relevant cybersecurity steerage into twelve main management teams and affords a high-level steerage on how every of the most important domains must be utilized. Every safety management outlines the way it must be established, validated, and launched throughout the organisation. For instance, when “Incident Administration” controls are talked about, BSC outlines how the method of figuring out, analysing, responding, and recovering from safety incidents must be documented and what sort of expertise or mechanism must be applied to guard confidentiality, integrity, or availability of the knowledge belongings. The BCS framework additionally outlines a guidelines that must be utilized inside each group.
Database Safety Commonplace (2020)
The customary goals to make sure that fundamental minimal safety controls are utilized for the database techniques and their customers similar to directors, builders, and database managers. It outlines a number of safety controls, particularly associated to databases, similar to the necessity to segregate duties or privileges of varied database customers to make sure that database `root` isn’t granted to low-level customers or enablement of encryption throughout the purposes speaking with the database. Particular safety controls similar to knowledge classification, change administration and audit must also be utilized to database servers.
Info Safety Administration Coverage (2019)
Relevant to all custodians of data on behalf of the Sultanate of Oman, this coverage outlines high-level data safety ideas that must be relevant to all organizations. It requires creation of Info Safety Committee which could encompass current steering committees or senior administration, taking care of knowledge inside any authorities group. The committee ought to oversee the event and implementation of safety program, relevant throughout the group, and implement particular steps similar to threat administration, knowledge classification, consciousness coaching, incident administration and enterprise continuity.
Cybersecurity Governance Pointers (2017)
This high-level guideline framework outlines the overview of varied cybersecurity governance ideas and requires regulated our bodies to determine cybersecurity governance inside group. The framework affords a steerage on how governance course of must be established throughout the enterprise, in a type of six key steps which purpose to assist in figuring out present, desired, and future state of cybersecurity inside a authorities group. The breakdown of the rules is as follows:
- Establish stakeholder wants: Organizations ought to determine the important thing stakeholders, their necessities, and expectations for cybersecurity programme that assist total enterprise mission and targets.
- Handle cybersecurity transformation technique: Includes defining the imaginative and prescient, authorized framework, targets, and targets for cybersecurity programme based mostly on understanding of present weaknesses and cybersecurity tradition inside a corporation.
- Outline cybersecurity construction: Includes establishing the governance construction, roles and duties (through RACI matrix), insurance policies and requirements, and processes and procedures for cybersecurity that must be applied going ahead. This step additionally requires involvement of steering committee which units the tone and path of cybersecurity transformation.
- Handle cybersecurity dangers: This step entails figuring out, assessing, treating and monitoring the cybersecurity dangers, in addition to implementing controls and measures to mitigate them based mostly on acceptable tolerance ranges.
- Optimize cybersecurity sources: This step requires allocation and administration of the human, monetary and technical sources for cybersecurity programme, in addition to making certain that accessible sources are aligned to anticipated targets that the programme is supposed to attain.
- Monitor cybersecurity effectiveness: This step entails measuring and evaluating the efficiency and effectives of a cybersecurity programme, in addition to reporting and speaking the outcomes and suggestions to steering committee and organizational administration.
Cloud and Internet hosting Companies Commonplace (2019)
Cloud and Internet hosting Companies Commonplace (CHSS) presents a breakdown of necessities relevant to Cloud Service Suppliers (CSP). At a excessive degree, the CSPs not solely must adjust to worldwide safety frameworks similar to ISO 27001, ISO27017 and ISO 270018 and management matrices offered by Cloud Safety Alliance (CSA) and PCI-DSS when internet hosting cost options. An vital emphasis of this framework is on how knowledge is dealt with, categorized, and saved inside a cloud setting and the way entry to such environments is offered. A CSP can also be to be accredited by a “Third-Social gathering Evaluation Group” which can audit, and entry compliance of cybersecurity controls associated to contingency planning, monitoring and the outcomes of varied assessments similar to penetration testing.
Overview of relevant legal guidelines, frameworks and rules
To raised reveal how every nation creates and applies cybersecurity rules the next desk was devised based mostly on accessible frameworks, regulation and relevant pointers on the time of scripting this weblog:
| State of Qatar | Kingdom of Saudi Arabia | Sultanate of Oman | |
|---|---|---|---|
| Relevant Regulation | Cybercrime Prevention Regulation (2014) Private Knowledge Safety Regulation (2016) | Anti-Cyber Crime Regulation (2007) Private Knowledge Safety Regulation (2023) | Cyber Safety Regulation (2019) Private Knowledge Safety Regulation (2023) |
| Nation-level Cybersecurity Technique Overview | The Nationwide Cyber Safety Technique (2014) The Nationwide Cyber Safety Technique (2024) | Nationwide Cybersecurity Technique (2019) | N/A |
| Frameworks, Pointers or Requirements relevant inside nation | Qatar Cybersecurity Framework (QCF) (2018) Nationwide Info Assurance Commonplace NIAS (2023) Nationwide Knowledge Classification Coverage (2023) The Nationwide Cyber Safety Technique (2014) The Nationwide Cyber Safety Technique (2024) | Important Cybersecurity Controls (ECC) (2018) Vital Methods Cybersecurity Controls (CSCC) (2019) Cloud Cybersecurity Controls (CCC) (2020) | Cybersecurity Governance Pointers (2017) Primary Safety Controls (2017) Info Safety Administration Coverage (2019) Cloud and Internet hosting Companies Commonplace (2019) Database Safety Commonplace (2020) |
| Regulatory Physique | Nationwide Cyber Safety Company | Nationwide Cybersecurity Authority | Cyber Defence Centre Ministry of Transport, Communications and Info Know-how (MTCIT) |
Conclusion
Though each listed nation launched their very own flavours of cybersecurity controls, unfold throughout many requirements, frameworks and legal guidelines, there are some commonalities between all nations talked about on this weblog submit:
- Every nation, though introducing a unique strategy to cybersecurity, bases the frameworks on three core ideas of cybersecurity – confidentiality, integrity and availability. No matter the nation, these ideas are evident within the regulation or frameworks, that are relevant throughout completely different sectors.
- The vary of safety controls every group should implement could differ relying on the criticality of the vertical the place this group operates. Though organizations, that are extra uncovered to delicate enterprise verticals similar to well being care or essential infrastructure (CI), may need barely completely different necessities for cybersecurity, most frameworks put an emphasis on steady identification, assessments and mitigation of potential cybersecurity threats. Cybersecurity is a steady course of and knowledge safety by no means stops, they should be upheld via common testing and assessments.
- Even with robust defences, cyber assaults can occur. Due to this fact, many requirements and frameworks require the deployment of technical measures like firewalls, endpoint controls, visibility and encryption. There are numerous organizational measures that may also be taken, similar to safety consciousness coaching and incident response procedures. It’s exceedingly uncommon {that a} one-size-fits-all strategy could be taken to create, for instance, acceptable indecent response procedures, therefore most frameworks put an emphasis on understanding the dangers or deficiencies and creation of personalized procedures that information the enterprise ideas to offer cybersecurity for his or her clients and customers. That is the place Talos Incident Response might help to organize these sorts of procedures that adjust to native frameworks and rules.
- Lively threat administration is usually anticipated by most frameworks and requirements and proactive strategy to figuring out, assessing, mitigating and monitoring potential threats and vulnerabilities is inspired or mandated. It’s not nearly establishing defenses and hoping for one of the best — it’s about actively in search of weaknesses, understanding the evolving risk panorama, and taking deliberate steps to reduce the consequences of potential cyberattacks.
- A few of these frameworks root their basic steerage and strategy in worldwide requirements similar to GDPR, NIST or ISO27001 whereas setting a baseline on which remaining controls will be constructed upon. In observe because of this if a corporation already employs fundamental NIST controls or are compliant with ISO27001 the appliance of further controls would possibly show to be a lot simpler train.
We’d love to listen to what you assume. Ask a Query, Remark Beneath, and Keep Linked with Cisco Safe on social!
Cisco Safety Social Channels
Share: